This article describes how to add authentication for a Fitbit account to an Azure AD B2C custom policy.
Architecture
The following diagram illustrates the authentication flow for a Fitbit account to an Azure AD B2C custom policy.
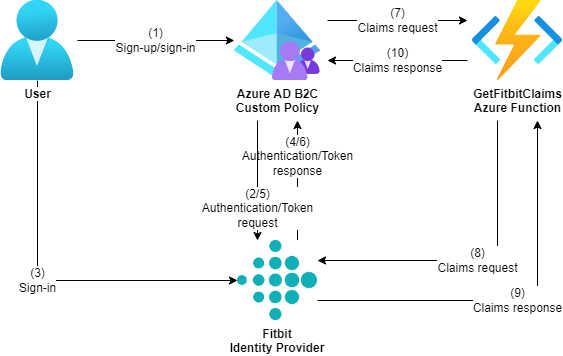
The authentication flow requires an Azure function that retrieves claims for the authenticated user.
For information about Fitbit and OAuth 2.0, see https://dev.fitbit.com/build/reference/web-api/developer-guide/authorization/.
Prerequisites
- If you don’t already have one, then you must create an Azure AD B2C tenant that is linked to your Azure subscription.
- Prepare your Azure AD B2C tenant by creating the token signing and encryption keys and creating the Identity Experience Framework applications.
- Download one of the starter packs for Azure AD B2C from Microsoft’s GitHub repository.
Create the Azure function
- Create a C# function containing the following code. This implements a GetFitbitClaims function that retrieves flattened claims for the authenticated user. Then publish this C# function to a function app.
using System;
using System.Net;
using System.Net.Http;
using System.Net.Http.Headers;
using System.Threading.Tasks;
using System.Web.Http;
using Microsoft.AspNetCore.Http;
using Microsoft.AspNetCore.Mvc;
using Microsoft.Azure.WebJobs;
using Microsoft.Azure.WebJobs.Extensions.Http;
using Microsoft.Extensions.Logging;
namespace SignInWithFitbit
{
public static class GetFitbitClaims
{
private static readonly HttpClient InnerClient = new HttpClient();
[FunctionName("GetFitbitClaims")]
public static async Task<IActionResult> Run(
[HttpTrigger(AuthorizationLevel.Anonymous, "get")] HttpRequest request,
ILogger logger)
{
if (!request.Headers.TryGetValue("Authorization", out var authorizationHeaderValues))
{
logger.LogError("The Authorization header is missing");
return new BadRequestResult();
}
if (authorizationHeaderValues.Count > 1)
{
logger.LogError("The Authorization header is invalid");
return new BadRequestResult();
}
var authorizationHeaderValue = authorizationHeaderValues[0];
var authorizationHeaderValueParts = authorizationHeaderValue.Split(' ');
if (authorizationHeaderValueParts.Length != 2 || !authorizationHeaderValueParts[0].Equals("Bearer", StringComparison.OrdinalIgnoreCase))
{
logger.LogError("The Authorization header is invalid");
return new BadRequestResult();
}
var innerRequest = new HttpRequestMessage(HttpMethod.Get, "https://api.fitbit.com/1/user/-/profile.json");
innerRequest.Headers.Authorization = new AuthenticationHeaderValue(authorizationHeaderValueParts[0], authorizationHeaderValueParts[1]);
var innerResponse = await InnerClient.SendAsync(innerRequest);
if (innerResponse.StatusCode != HttpStatusCode.OK)
{
return new InternalServerErrorResult();
}
var innerResponseModel = await innerResponse.Content.ReadAsJsonAsync<FitbitClaimsResponseModel>();
var responseModel = new
{
id = innerResponseModel.User?.EncodedId,
name = innerResponseModel.User?.FullName
};
return new OkObjectResult(responseModel);
}
}
}
The model classes are implemented as follows.
using Newtonsoft.Json;
namespace SignInWithFitbit
{
public class FitbitClaimsResponseModel
{
[JsonProperty(PropertyName = "user")]
public FitbitUserModel User { get; set; }
}
public class FitbitUserModel
{
[JsonProperty("encodedId")]
public string EncodedId { get; set; }
[JsonProperty("fullName")]
public string FullName { get; set; }
}
}
The ReadAsJsonAsync extension method is implemented as follows.
using System.Net.Http;
using System.Threading.Tasks;
using Newtonsoft.Json;
namespace SignInWithFitbit
{
public static class HttpContentExtensions
{
public static async Task<T> ReadAsJsonAsync<T>(this HttpContent content)
{
if (content == null)
{
return default;
}
var value = await content.ReadAsStringAsync();
return JsonConvert.DeserializeObject<T>(value);
}
}
}
Configure a Fitbit application
- Log in to https://dev.fitbit.com/apps.
- On the Applications page, select Register a new app.
- In the Register an application page, enter the following fields and then select Register:
- Application Name
- Description
- Application Website URL
- Organization
- Organization Website URL
- Terms of Service URL
- Privacy Policy URL
- OAuth 2.0 Application Type: Server
- Redirect URL: Enter either https://your-tenant-name.b2clogin.com/your-tenant-name.onmicrosoft.com/oauth2/authresp if you use the built-in domain or https://your-domain-name/your-tenant-name.onmicrosoft.com/oauth2/authresp if you use a custom domain for the Redirect URL field. Replace your-tenant-name with your tenant name and your-domain-name with your custom domain.
- Default Access Type: Read Only
- On the application page, copy the OAuth 2.0 Client ID and Client Secret fields.
Add the client secret for the Fitbit application as a policy key
- Sign in to the Azure AD B2C portal.
- Select Identity Experience Framework.
- Select Policy keys.
- Select Add.
- In the Create a key section, enter the following fields and then select Create:
- Options:
Manual - Name:
FitbitClientSecret - Secret: Paste the Client Secret field that was copied in the previous section.
- Options:
Configure Fitbit as an identity provider
- Open the TrustFrameworkExtensions.xml file.
- Find the ClaimsProviders element. If it doesn’t exist, then add it to the TrustFrameworkPolicy element.
- Add the following ClaimsProvider element to the ClaimsProviders element. Replace
your-fitbit-client-idwith the OAuth 2.0 Client ID field that was copied in the Configure a Fitbit application section. Replaceyour-function-app-namewith the function app name that was created in the Create the Azure function section.
<ClaimsProvider>
<Domain>fitbit.com</Domain>
<DisplayName>Fitbit</DisplayName>
<TechnicalProfiles>
<TechnicalProfile Id="Fitbit-OAuth2">
<DisplayName>Fitbit</DisplayName>
<Protocol Name="OAuth2" />
<Metadata>
<Item Key="client_id">your-fitbit-client-id</Item>
<Item Key="authorization_endpoint">https://www.fitbit.com/oauth2/authorize</Item>
<Item Key="AccessTokenEndpoint">https://api.fitbit.com/oauth2/token</Item>
<Item Key="ClaimsEndpoint">https://your-function-app-name.azurewebsites.net/api/GetFitbitClaims</Item>
<Item Key="scope">profile</Item>
<Item Key="HttpBinding">POST</Item>
<Item Key="token_endpoint_auth_method">client_secret_basic</Item>
<Item Key="BearerTokenTransmissionMethod">AuthorizationHeader</Item>
<Item Key="UsePolicyInRedirectUri">false</Item>
</Metadata>
<CryptographicKeys>
<Key Id="client_secret" StorageReferenceId="B2C_1A_FitbitClientSecret" />
</CryptographicKeys>
<OutputClaims>
<OutputClaim ClaimTypeReferenceId="authenticationSource" DefaultValue="socialIdpAuthentication" AlwaysUseDefaultValue="true" />
<OutputClaim ClaimTypeReferenceId="identityProvider" DefaultValue="fitbit.com" AlwaysUseDefaultValue="true" />
<OutputClaim ClaimTypeReferenceId="issuerUserId" PartnerClaimType="id" />
<OutputClaim ClaimTypeReferenceId="displayName" PartnerClaimType="name" />
</OutputClaims>
<OutputClaimsTransformations>
<OutputClaimsTransformation ReferenceId="CreateRandomUPNUserName" />
<OutputClaimsTransformation ReferenceId="CreateUserPrincipalName" />
<OutputClaimsTransformation ReferenceId="CreateAlternativeSecurityId" />
</OutputClaimsTransformations>
<UseTechnicalProfileForSessionManagement ReferenceId="SM-SocialLogin" />
</TechnicalProfile>
</TechnicalProfiles>
</ClaimsProvider>
Add a user journey
- Open the TrustFrameworkBase.xml file.
- Copy the UserJourney element that includes
Id="SignUpOrSignIn". - Open the TrustFrameworkExtensions.xml file and find the UserJourneys element. If it doesn’t exist, then add it to the TrustFrameworkPolicy element.
- Paste the UserJourney element that was copied in step 2 to the UserJourneys element and replace the Id attribute for this UserJourney element from
"SignUpOrSignIn"to"FitbitSignUpOrSignIn".
Add the identity provider to the user journey
- Add the claims provider that was configured in the Configure Fitbit as an identity provider section to the user journey that was added in the previous section.
<OrchestrationStep Order="1" Type="CombinedSignInAndSignUp" ContentDefinitionReferenceId="api.signuporsignin">
<ClaimsProviderSelections>
...
<ClaimsProviderSelection TargetClaimsExchangeId="FitbitExchange" />
</ClaimsProviderSelections>
...
</OrchestrationStep>
<OrchestrationStep Order="2" Type="ClaimsExchange">
...
<ClaimsExchanges>
<ClaimsExchange Id="FitbitExchange" TechnicalProfileReferenceId="Fitbit-OAuth2" />
</ClaimsExchanges>
...
</OrchestrationStep>
Configure the relying party policy
- Open the SignUpOrSignIn.xml file.
- Replace the ReferenceId attribute for the DefaultUserJourney element from
"SignUpOrSignIn"to".Fitbit
<RelyingParty>
<DefaultUserJourney ReferenceId="FitbitSignUpSignIn" />
...
</RelyingParty>
Upload and test the custom policy
- Upload all policy files in the following order to your Azure AD B2C tenant:
- TrustFrameworkBase.xml
- TrustFrameworkLocalization.xml
- TrustFrameworkExtensions.xml
- SignUpOrSignIn.xml
- Test the B2C_1A_signup_signin policy from your Azure AD B2C tenant.






